This week at CodeRanch we have a promotion for Iron Clad Java. Before the promo, I wanted to make sure we didn’t have anything embarrassing going on. We had already dealt with XSS, CSRF, Clickjacking and brute force logins. As I looked through the OWASP Top 10, I realized that I had no idea how we were doing on A9 “Using Components with Known Vulnerabilities”.
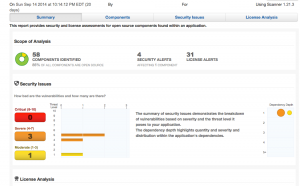
I saw that Sonatype provides a free Insight scan. I did that and got a nice summary:
The high points of the summary are that:
- We use 58 libraries
- No high known security vulnerabilities in the libraries we use!
- Need to look into the details for the license “issues” since we are non-commerical.
Details
I then clicked on the other tabs and got a sample report. That’s the line where free lives. Since CodeRanch doesn’t have a budget, I asked the vendor for a free credit to see the report and they graciously agreed.
I then learned:
- All four of our security “issues” were in commons-httpclient. This library isn’t used anywhere in the codebase or in unit tests. I checked the description of the issue and we don’t use that part of the library. So clean! I’m impressed that a completely volunteer run site came out clean. Good job to all the mods who update the jars!
- The license part showed a variety of licenses. For example dom4j and hibernate-core came up. The licenses would be more useful if we were a company and owned the product/could configure it ourselves.
- It was cool seeing the ages of the components we use. And which ones are exact matches vs similar. (I’m sure we didn’t edit hibernate-core!)
This report would be clearly be more useful for a large company. More applications and more people who work on them makes it harder to know what is going on. Still, I’m glad I didn’t have to check 50+ libraries by hand.
Disclaimer: I received free access to the detailed report in exchange for writing this review.